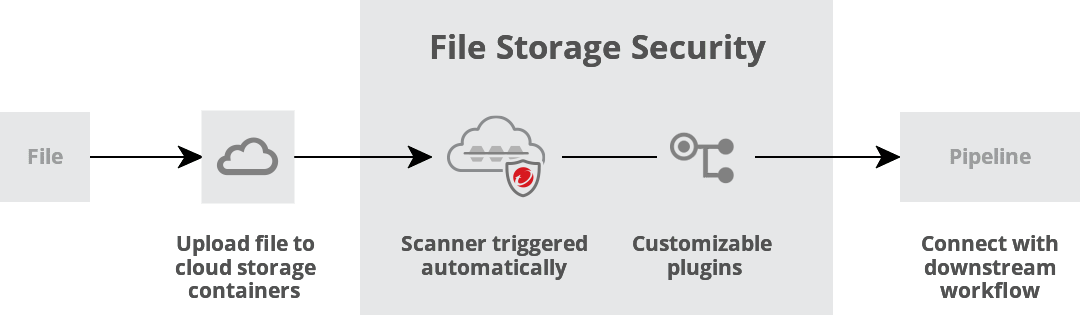
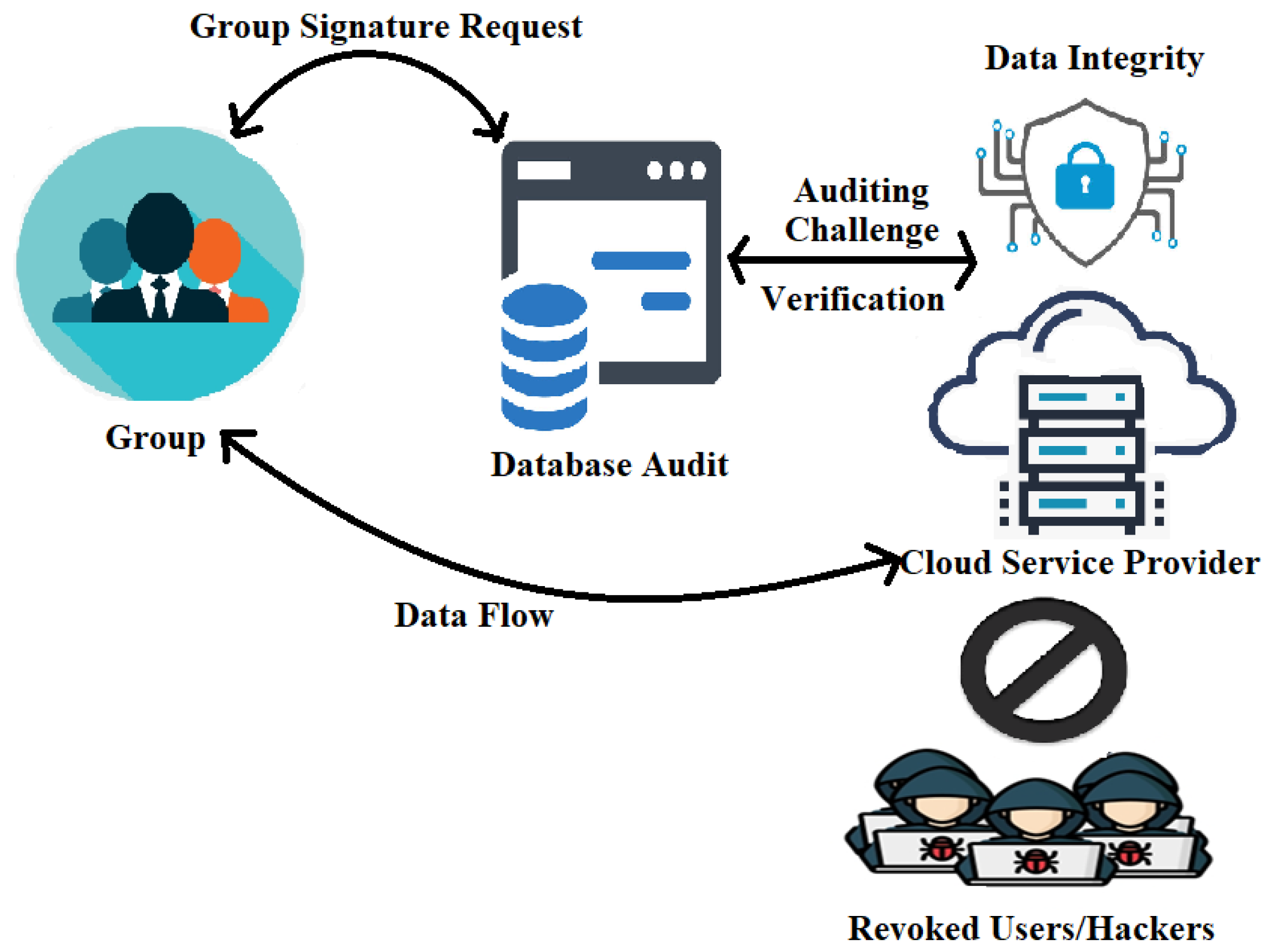
Figure 1 from Data Security Algorithms for Cloud Storage System using Cryptographic Method | Semantic Scholar

Enhanced data storage security in cloud environment using encryption, compression and splitting technique | Semantic Scholar

Cloud storage security - CISSP Cert Prep (2021): 2 Asset Security Video Tutorial | LinkedIn Learning, formerly Lynda.com
Electronics | Free Full-Text | Enhanced Cloud Storage Encryption Standard for Security in Distributed Environments